XMsg Lifecycle
Flow Diagram
The following steps provide a comprehensive overview of how an XMsg travels from a source rollup VM to a destination rollup VM. This process is visualized in Figure 4.
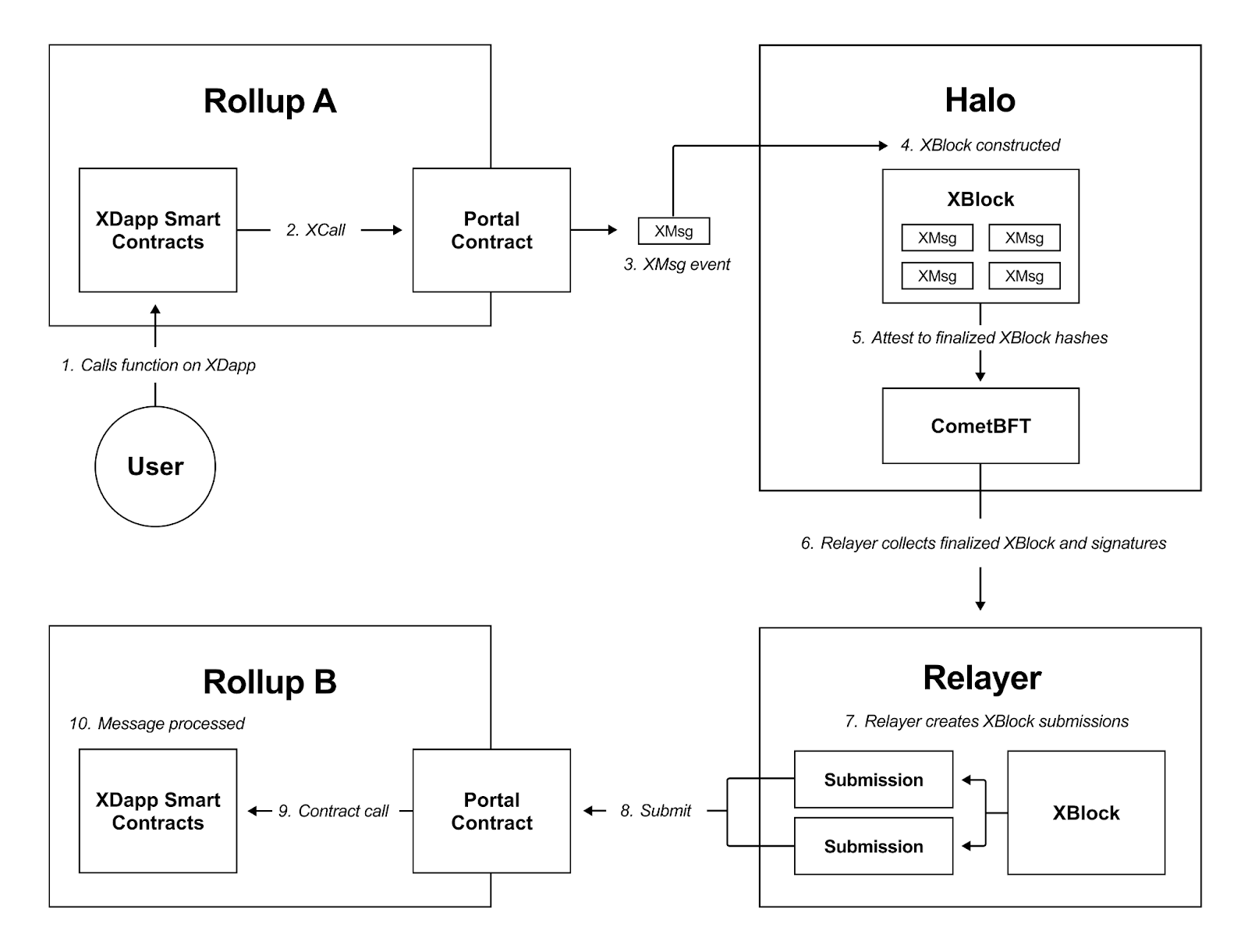
XMsg through the networkSteps
1. User Call
- A user calls an xapp smart contract function on a rollup VM.
2. Smart Contract Logic
-
The smart contract converts the user’s logic into an
xcallthat is made on the rollup VM’s Portal contract.xcallare defined in Solidity as below (read more in the develop section):omni.xcall(
uint64 destChainId, // desintation chain id
address to, // contract address on the dest rollup to execute the call on
bytes memory data // calldata for the transaction, abi encoded
)
3. Portal Contract Event Emission
-
The Portal contract converts the
xcallinto anXMsgand emits the correspondingXMsgevent.XMsgevents are defined in Solidity as:event XMsg (
address SourceMsgSender // Sender on source chain, set to msg.Sender
uint256 XStreamOffset // Monotonically incremented offset of XMsg in the XStream
uint256 DestChainID // Target chain ID as per https://chainlist.org/
address DestAddress // Target/To address to "call" on destination chain
bytes Data // Data to provide to "call" on destination chain
uint256 DestGasLimit // Gas limit to use for "call" on destination chain
)
4. Validator XMsg Packaging
-
Validators package multiple
XMsginto anXBlock. It is a deterministic one-to-one mapping. Inhalo,XBlockare typed as:// XBlock represents the cross-chain properties of a source chain finalised block.
type XBlock (
uint SourceChainID // Source chain ID as per https://chainlist.org
uint BlockHeight // Height of the source chain block
bytes32 BlockHash // Hash of the source chain block
XMsg[] Msgs // XMsg events included in the source block.
XReceipt[] Receipts // XReceipt events included in the source block.
)XBlockstructure provides the following properties to the Omni Network:- Succinctly verifiable merkle-multi-proofs for sub-ranges of
XMsgper source-target pair allowing relayers to manage submission costs at singleXMsggranularity. - Omni Consensus attestations are not required for source chain blocks without any cross chain messages (aka empty
XBlock). - Relayer submissions are not required on destination chains for batches without cross chain messages.
- The logic to create a
XBlockis deterministic for any finalized source chain block height.
XBlockStorage and CalculationXBlockis not stored as they are deterministically calculated from a source blockchain. So in effect, the source blockchain stores them. Any component that depends onXBlock, calculates it from a source chain.where is a deterministic
purefunction that takes a finalized blockchain as input and producesXBlockas output. In practice, source blocks can be streamed and transformed using a simple translation function backed by an in-memory cache.XMsgare associated with anXStream. AnXStreamis a logical connection between a source and destination chain. It contains manyXMsg, each with a monotonically incrementingXStreamOffset(the offset is like a EOA nonce, it is incremented for each subsequent message sent from a source chain to a destination chain).XMsgare therefore uniquely identified and strictly ordered by their associatedXStreamandXStreamOffset.XStreamOffsetallows for exactly-once delivery guarantees with strict ordering per source-destination chain pair. - Succinctly verifiable merkle-multi-proofs for sub-ranges of
5. Validator Attestation
-
Validators attest to
XBlockhashes during consensus. Each Omni consensus layer validator monitors every finalized block for all source chains inhalo. Validators need to wait for block finalization, or some other agreed-upon threshold, to ensure consistent and secure cross-chain messaging.haloattests via CometBFT vote extensions, all validators in the CometBFT validator set should attest to allXBlock(in addition to their normal validator duties). An attestation is defined by the followingAttestationtype:type Attestation (
// Composite primary key of XBlock + ValSet
uint SourceChainID // SourceChainID of the XBlock
uint BlockHeight // Source chain block height
bytes32 BlockHash // Source chain block hash
uint ValidatorSetID // Unique identifier of current validator set
bytes32 XBlockRoot // Merkle root of the XBlock
bytes32 ValidatorPubkey // Validator identifier
bytes32 Signature // Validator signature of XBlockHash
)Validators return an array of
Attestationduring the ABCI++ExtendVotemethod.
6. Relayer Collects XBlocks
-
Relayers monitoring the Omni consensus layer gather finalized
XBlockhashes and their correspondingXBlockandXMsg. Finalized blocks without anyXMsgevents are ignored. The Relayer submitsXMsgs to destination chain that have ⅔ of validator signatures.For each destination chain, the relayer decides how many
XMsgto submit, which defines the “cost” of transactions being submitted to the destination chain. This is primarily defined by the data size and gas limit of the messages and the portal contract verification and processing overhead.A merkle-multi-proof is generated for the set of identified
XMsgthat match the quorumXBlockattestations root. The relayer submits an EVM transaction to the destination chain, ensuring it gets included on-chain as soon as possible. The transaction contains the following data:type Submission (
AggregateAttestation att // Aggregate attestation containing quorum signatures for a specific validator set.
XMsg[] msgs // Subset of XMsgs in a XBlock (could also be all)
bytes Proofs // Merkle-multi-proof for XMsgBatch
)
7. Relayer Submits XBlocks
- For every finalized
XBlockhash, relayers construct anXBlocksubmission containing theXBlockand the validator signatures for theXBlockhashes. Merkle proofs are generated to prove the inclusion of eachXMsgin theXBlockhash. This ensures the decoupling of attestations from execution, thereby allowing the relayer to split the execution of anXBlockinto many transactions so that it adheres to the constraints of the destination rollup VM.
8. Relayer Submits XMsg
-
The relayer delivers its submissions to the Portal contract on the destination rollup VM. Relayer submissions are defined in Go as:
// Submission is a cross-chain submission of a set of messages and their proofs.
type Submission struct {
AttestationRoot common.Hash // Merkle root of the attestations
ValidatorSetID uint64 // Unique identified of the validator set included in this aggregate.
BlockHeader BlockHeader // BlockHeader identifies the cross-chain Block
Msgs []Msg // Messages to be submitted
Proof [][32]byte // Merkle multi proofs of the messages
ProofFlags []bool // Flags indicating whether the proof is a left or right proof
Signatures []SigTuple // Validator signatures and public keys
DestChainID uint64 // Destination chain ID, for internal use only
}
9. Portal Verification and Forwarding
-
The receiving Portal contract verifies the
XBlock’s validator signatures andXMsgmerkle proofs before passing all verifiedXMsgs to their destination smart contracts on the rollup VM. After validating and processing the submittedXMsg, the portal contract emits anXReceiptevent. This marks theXMsgas “successful” or “reverted” byhalo.XMsgcan revert if the gas limit was exceeded or if target address smart contract logic reverted for other reasons.XReceiptare included inXBlock(same asXMsg).type XReceipt (
uint SourceChainID // The cross-chain message's source chain
uint XStreamOffset // Offset of XMsg in the XStream
uint GasUsed // Gas used dueing message "call"
uint Result // 0 for success, 1 for revert
address RelayerAddress // Address of relayer that submitted the message
)
10. Smart Contract Execution
- The receiving smart contracts execute the logic for their users.